Fresh install of OS and MythTV on n43
Created 2007/09/05 – last revised 2008/01/06
I needed to upgrade MythTV to 0.20.2 due to the demise of Zap2It schedules, but I didn’t have another system which matched the hardware used on my MythTV PVR. So I installed a spare 120GB EIDE and started from scratch to build another MythTV instance from scratch. Once I was satisfied the new instance would pass the SAT (spouse approval test), I used LVM to move everything over to the 320GB SATA disk which currently contains the old (production) MythTV sw and configuration.
This describes that build and migration process.
Hardware (n43):
Antec Fusion HTPC case

AMD Sempron processor (about 1.6GHz)
512MB memory – good enough for single tuner and OS
Hauppage PVR-350 standard definition capture card
Integrated on to mainboard:
Audio:
ALC883 PCM nVidia MCP51 controller – kernel module snd-hda-intel (high definition audio)
Video:
nVidia C51 – Quadro NVS 210S / GeForce 6150LE
nVidia EIDE and SATA controller – …
1. Install OS
Seems to be lots of hits on Fedora 7 and MythTV, as well the reading I’ve done on Fedora 7 seems to show it can be easily kept up to date (via yum) – and it has the OS clustering capabilities as part of the base now, which I’ll use when I split the current single system making it the back end and adding a silent (diskless) front end.
Downloaded and burnt Fedora 7 i386 DVD. For future options, extracted and burnt boot.iso … also see notes on how to install Fedora 7 via boot.iso and NFS. (notes to be added)
Disabled SATA hdd in BIOS (could have unplugged it, but easier to just disable via sw).
Used DVD drive in n43 to install Fedora 7 on the temporary EIDE drive.
Select packages for install:
MySQL Server
Web Server
See scripts for automated Fedora 7 OS setup and package install (setup1.shl, setup2.shl) (scripts to be added)
About 25 min off DVD for base load
Setup (first time boot):
Firewall – allow SSH and HTTP, otherwise no inbound services other than ESTABLISHED,RELATED are needed at this point. Will open MySQL and ICMP for monitoring purposes later. When this system becomes the MythTV backend, will have to add MythTV ports (see FAQ).
SELinux – disable, will add SE configuration at some future point.
NTP – use default Fedora 7 NTP service configuration, time sync is obviously very important (unless you don’t want your recordings to start/end at the right times).
MythTV seems to heavily use KDE, so although Gnome is default, may need to use KDE. I selected Gnome this time. And KDE this time. And RatPoison is a compact window manager which may be easier to configure for mythtv. Finally I’m using fvwm2 .. more on that later.
Update /etc/hosts
192.168.2.143 mythtv.networkforensics.org mythtv n43
Manually set the interface speed/duplex (gigabit interface doesn’t do well in autonegotiate – poor performance, but no interface errors). Will come back and setup an init script.
# ethtool -s eth0 speed 100 duplex full
Add ATrpms repository into yum configuration:
NOTE: other ATrpm yum configurations on the net don’t work!
– add the following into /etc/yum.conf
[atrpms]
name=Fedora Core $releasever – $basearch – ATrpms
baseurl=http://dl.atrpms.net/f$releasever-$basearch/atrpms/stable
gpgkey=http://ATrpms.net/RPM-GPG-KEY.atrpms
gpgcheck=1
Import ATrpms key
# rpm –import http://ATrpms.net/RPM-GPG-KEY.atrpms
Disable ATrpms repository, so we only get mythtv packages from it:
– add the following to the atrpms section just added to the /etc/yum.conf:
enabled=0
Update the packages to current using the standard Fedora repositories
When following the Fedora / MythTV HOWTO (http://wilsonet.com/mythtv), they use variable KVER which is just uname -r
# echo “export KVER=\\`uname -r\\`” >> /etc/profile.d/kver.sh
Do yum upgrade to get latest kernel and system
# yum upgrade
464MB 265 packages
<odd>
Kernel panic during reboot after upgrade
Searched on “2.6.22 fedora 7 kernel panic noapic” – lots of suggestions but doing a single boot again, while interrupting the grub boot and adding noapic to the end of the kernel boot line seemed to fix it. Now the grub.conf looks like (note the vga=791 arg):
default=0
timeout=5
splashimage=(hd0,0)/grub/splash.xpm.gz
hiddenmenu
title Fedora (2.6.22.4-65.fc7)
root (hd0,0)
kernel /vmlinuz-2.6.22.4-65.fc7 ro root=/dev/VolGroup00/LogVol00 rhgb quiet vga=791
initrd /initrd-2.6.22.4-65.fc7.img
title Fedora (2.6.21-1.3194.fc7)
root (hd0,0)
kernel /vmlinuz-2.6.21-1.3194.fc7 ro root=/dev/VolGroup00/LogVol00 rhgb quiet vga=791
initrd /initrd-2.6.21-1.3194.fc7.img
Add window manager fvwm here – comes from Fed
ora repo
# yum install fvwm2
2. No mouse cursor in Gnome
Seems the nVidia graphics are broken somehow. Must disable hardware cursor?
<URL>
ok add this line to your xorg.conf
Option “HWCursor” “off”
so it looks something like this
Code:
Section "Device"
BoardName "GeForce 6600/GeForce 6600 GT"
BusID "1:0:0"
Driver "nvidia"
Identifier "Device[0]"
Option "HWCursor" "off"
Screen 0
VendorName "NVidia"
EndSection
logged out from Gnome, causes an X restart then the mouse cursor showed up properly.
3. Set Monitor and Resolution
In gnome, I manually set the monitor, it could not autodetect the Viewsonic Optiquest V75. Restarted X, had to set the resolution (it defaulted to way too high of a setting)
HOLD:
As per Fedora MythTV setup guide, install the nVidia drivers:
# yum -y install nvidia-graphics9755-kmdl-$KVER
# yum -y install nvidia-graphics9755-libs nvidia-graphics9755
Actually, this is done now by copying in a revised xorg.conf
[root@mythtv grub]# cat /etc/X11/xorg.conf.1024×768-monitor-only-V75-BEST
# Xorg configuration created by system-config-display
Section “ServerLayout”
Identifier “single head configuration”
Screen 0 “Screen0” 0 0
InputDevice “Keyboard0” “CoreKeyboard”
EndSection
Section “InputDevice”
Identifier “Keyboard0”
Driver “kbd”
#Option “XkbModel” “pc105”
Option “XkbModel” “pc101”
Option “XkbLayout” “us”
EndSection
Section “Monitor”
Identifier “Monitor0”
ModelName “Monitor 1280×1024”
HorizSync 31.5 – 79.0
VertRefresh 50.0 – 90.0
Option “dpms”
EndSection
Section “Device”
Identifier “Videocard0”
Driver “nv”
Option “HWCursor” “off”
EndSection
Section “Screen”
Identifier “Screen0”
Device “Videocard0”
Monitor “Monitor0”
DefaultDepth 24
SubSection “Display”
Viewport 0 0
Depth 24
Modes “1024×768” “800×600” “720×400” “640×480” “640×400” “640×350”
EndSubSection
EndSection
Turn off screen saver
Disable unnecessary services
services=”avahi pcps bluetooth”
for service in $services; do chkconfig $service off; service $service stop; done
avahi – DNS service discovery
pcps – smart card daemon
bluetooth
4. Set mysql to start on boot
chkconfig mysqld on
5. Start up MySQL
service mysqld start
6. Set MySQL root password
mysql –uroot
mysql> grant all on *.* to root@localhost identified by “rootpassword” with grant option;
mysql> grant all on *.* to root@n43 identified by ‘rootpassword’ with grant option;
7. Create MythTV database
Test out mysql connection, user, password
# mysql -uroot -prootpassword
mysql>
Run MythTV database setup
# mysql -uroot -prootpassword < /usr/share/mythtv/sql/mc.sql
/usr/share/mythtv/sql/mc.sql:
CREATE DATABASE if not exists mythconverg;
GRANT ALL ON mythconverg.* TO mythtv@localhost IDENTIFIED BY “mythtv”;
FLUSH PRIVILEGES;
GRANT CREATE TEMPORARY TABLES ON mythconverg.* TO mythtv@localhost
IDENTIFIED BY “mythtv”;
FLUSH PRIVILEGES;
ALTER DATABASE mythconverg DEFAULT CHARACTER SET latin1;
8. Install MythTV Suite
# yum –enable=atrpms install mythtv-suite
122 packages, 105MB
Create directory for recordings
# mkdir /storage/recordings
# chown mythtv:mythtv /storage/recordings
9.
Install ivtv drivers and firmware for PVR-350
# yum –enable=atrpms install ivtv-firmware
# yum –enable=atrpms install ivtv-kmdl-$KVER
10. Update modprobe.conf to enable TV Out on PVR-350
# load ivtv-fb for PVR-350 output
install ivtv /sbin/modprobe –ignore-install ivtv; /sbin/modprobe ivtv-fb
Manually load ivtv
# /sbin/depmod -a
# /sbin/modprobe ivtv
Manually tried to load ivtv-fb – segfaulted … see the part of the howto on modifying grub boot loader…
We’re going to make little modification to the kernel boot line in your grub.conf file that should force the ivtv frame buffer to load on /dev/fb1, as well as allow the ivtv-fb module to be loaded and unloaded. Without doing this, unloading the ivtv-fb module would probably crash your system. To the end of all ‘kernel /vmlinuz…’ lines in /boot/grub/grub.conf, append ‘vga=791’, then reboot your system. This tells the kernel to load a frame buffer for your video card at 1024×768, 16-bit color. I use this all the time myself, simply so I can see more when I’m not in X. I’d always done this on my 350-equipped box without even thinking about it, which could explain some of why I’ve not run into some of the problems other folks have…
Note video device:
[root@mythtv ~]# ls -l /dev/video*
lrwxrwxrwx 1 root root 6 2007-09-09 18:17 /dev/video -> video0
crw——- 1 root root 81, 0 2007-09-09 18:17 /dev/video0
crw——- 1 root root 81, 16 2007-09-09 18:17 /dev/video16
crw——- 1 root root 81, 24 2007-09-09 18:17 /dev/video24
crw——- 1 root root 81, 32 2007-09-09 18:17 /dev/video32
crw——- 1 root root 81, 48 2007-09-09 18:17 /dev/video48
[root@mythtv ~]#
From dmesg:
ivtv0: Registered device video0 for encoder MPEG (4 MB)
ivtv0: Registered device video32 for encoder YUV (2 MB)
ivtv0: Registered device vbi0 for encoder VBI (1 MB)
ivtv0: Registered device video24 for encoder PCM audio (1 MB)
ivtv0: Registered device radio0 for encoder radio
ivtv0: Registered device video16 for decoder MPEG (1 MB)
ivtv0: Registered device vbi8 for decoder VBI (1 MB)
ivtv0: Registered device vbi16 for decoder VOUT
ivtv0: Registered device video48 for decoder YUV (1 MB)
11. Test out PVR-350 TV Out
As per https://help.ubuntu.com/community/MythTV_Edgy_hardware_pvr-350_TV-out
Try to display the TV test pattern by putting the saa7127 module into test mode:
# /sbin/rmmod saa7127
# /sbin/modprobe saa7127 test_image=1
Works!
Resume normal operation:
# rmmod saa7127
# modprobe saa7127
Test video capture
# /usr/bin/v4l2-ctl -i 0
12. Manually compile ivtv module for X
Had to manually compile ivtv driver for x to enable tv out .. due to some 2.6.22 issue.
As per README in ivtv x driver package – must install xorg sdk to allow compile:
# yum install xorg-x11-server-sdk
Then compile the new ivtv xdriver:
# sh ./configure
# make
# make install
Copy into xorg directory:
# cp /usr/local/lib/xorg/modules/drivers/ivtv_drv.so /usr/lib/xorg/modules/drivers
if gdm failed, ps -ef , then kill it to restart
copy in new xorg.conf (with TV Out section) and do <ctrl><alt><backspace> to restart x server
[root@mythtv ~]# cat /etc/X11/xorg.conf.tvout
# XFree86 4 configuration created by pyxf86config
Section “ServerLayout”
Identifier “Default Layout”
Screen 0 “Screen0” 0 0
InputDevice “Mouse0” “CorePointer”
InputDevice “Keyboard0” “CoreKeyboard”
EndSection
Section “Files”
# RgbPath is the location of the RGB database. Note, this is the name of the
# file minus the extension (like “.txt” or “.db”). There is normally
# no need to change the default.
# Multiple FontPath entries are allowed (they are concatenated together)
# By default, Red Hat 6.0 and later now use a font server independent of
# the X server to render fonts.
RgbPath “/usr/X11R6/lib/X11/rgb”
# ModulePath “/usr/X11R6/lib/modules/extensions/nvidia”
# ModulePath “/usr/X11R6/lib/modules/extensions”
# ModulePath “/usr/X11R6/lib/modules”
FontPath “unix/:7100”
EndSection
Section “Module”
Load “dbe”
Load “extmod”
Load “fbdevhw”
Load “glx”
Load “record”
Load “freetype”
Load “type1”
EndSection
Section “InputDevice”
# Specify which keyboard LEDs can be user-controlled (eg, with xset(1))
# Option “Xleds” “1 2 3”
# To disable the XKEYBOARD extension, uncomment XkbDisable.
# Option “XkbDisable”
# To customise the XKB settings to suit your keyboard, modify the
# lines below (which are the defaults). For example, for a non-U.S.
# keyboard, you will probably want to use:
# Option “XkbModel” “pc102”
# If you have a US Microsoft Natural keyboard, you can use:
# Option “XkbModel” “microsoft”
#
# Then to change the language, change the Layout setting.
# For example, a german layout can be obtained with:
# Option “XkbLayout” “de”
# or:
# Option “XkbLayout” “de”
# Option “XkbVariant” “nodeadkeys”
#
# If you’d like to switch the positions of your capslock and
# control keys, use:
# Option “XkbOptions” “ctrl:swapcaps”
# Or if you just want both to be control, use:
# Option “XkbOptions” “ctrl:nocaps”
#
Identifier “Keyboard0”
Driver “keyboard”
Option “XkbRules” “xfree86”
#Option “XkbModel” “pc105”
Option “XkbModel” “pc101”
Option “XkbLayout” “us”
EndSection
Section “InputDevice”
Identifier “Mouse0”
Driver “mouse”
Option “Protocol” “IMPS/2”
Option “Device” “/dev/input/mice”
Option “ZAxisMapping” “4 5”
Option “Emulate3Buttons” “no”
EndSection
Section “InputDevice”
# If the normal CorePointer mouse is not a USB mouse then
# this input device can be used in AlwaysCore mode to let you
# also use USB mice at the same time.
Identifier “DevInputMice”
Driver “mouse”
Option “Protocol” “IMPS/2”
Option “Device” “/dev/input/mice”
Option “ZAxisMapping” “4 5”
Option “Emulate3Buttons” “no”
EndSection
Section “Monitor”
Identifier “NTSC Monitor”
HorizSync 30-68
VertRefresh 50-120
Mode “720×480”
# D: 34.563 MHz, H: 37.244 kHz, V: 73.897 Hz
DotClock 34.564
HTimings 720 752 840 928
VTimings 480 484 488 504
Flags “-HSync” “-VSync”
EndMode
EndSection
Section “Device”
Identifier “Hauppauge PVR 350 iTVC15 Framebuffer”
#Driver “ivtvdev”
# 2007/09/09 ACP – changed to ivtv
Driver “ivtv”
### change fb1 to whatever your card grabbed
Option “fbdev” “/dev/fb1”
Option “ivtv” “/dev/fb1”
### change the BusID to whatever is reported by lspci,
### converted from hex to decimal
BusID “PCI:4:6:0” # lspci says 00:08.0
### More examples
#BusID “PCI:0:10:0” # lspci says 00:0a.0
#BusID “PCI:1:14:0” # lspci says 01:0e.0
#BusID “PCI:0:5:1” # lspci says 00:05.1
EndSection
Section “Screen”
Identifier “Screen0”
Device “Hauppauge PVR 350 iTVC15 Framebuffer”
Monitor “NTSC Monitor”
DefaultDepth 24
DefaultFbbpp 32
Subsection “Display”
Depth 24
FbBpp 32
Modes “720×480”
EndSubsection
EndSection
Section “DRI”
Group 0
Mode 0666
EndSection
13. Run mythtv-setup
Blank menu ..
Check out http://www.gossamer-threads.com/lists/mythtv/users/286856
I found this simple set of directions to add in a base set of true
type fonts (which includes Ariel) to Fedora 7 and it solved the problem.
1. Open a Terminal and cd to a directory you can work in
2. Become root
3. Download the MS Core Fonts Smart Package File
wget http://corefonts.sourceforge.net/msttcorefonts-2.0-1.spec
4. Make sure that the rpm-build and cabextract packages are installed
yum install rpm-build cabextract
5. Build the Core Fonts package:
rpmbuild -ba msttcorefonts-2.0-1.spec
6. Install the Core Fonts package
rpm -Uvh /usr/src/redhat/RPMS/noarch/msttcorefonts-2.0-1.noarch.rpm
The web site I found this one was: http://www.fedorafaq.org/#installfonts
Sign in as mythtv
$ mythtv-setup
Setup Video Capture cards, listing source, channel setup
$ mythfilldatabase
Setup remote control
Go get the LIRC packages from ATrpms
# yum –enable=atrpms install lirc-0.8.3
And get the kernel modules:
# yum –enable=atrpms install lirc-kmdl-2.6.22.4-65.fc7-0.8.3-70_cvs20070827.fc7
resulted in:
Installed: lirc-kmdl-2.6.22.4-65.fc7.i686 0:0.8.3-70_cvs20070827.fc7
Dependency Installed: lirc-devices.noarch 0:0.8-4.fc7
Manual test:
# modprobe lirc_mceusb2
Update modprobe.conf to load LIRC
…
/dev/lirc was symlinked to /dev/lirc/0 (which is the PVR-350 …) so re-linked to /dev/lirc/1 and restarted lircd
# service lircd restart
then irw showed button presses!
Updated /etc/init.d/lircd to relink the /dev/lirc symlink to /dev/lirc/1
Get MythTV to use remote:
Copy lircrc file into ~mythtv/.mythtv/lircrc and ~mythtv/lircrc (no dots)
Install lirc kernel modules
NO yum –enable atrpms install lirc-kmdl-2.6.22.4-65.fc7
Had to uninstall all the modules I installed then re-install lirc 0.8.3 from atrpms
Page on the Microsoft MCE remote: http://www.mythtv.org/wiki/index.php/MCE_Remote
Setup (tune) screen size
Overscan (image off the screen)
http://www.mythtv.org/wiki/index.php/Overscan
on Toshiba tv (pixels):
width 632
height 436
GUI x offset 36
GUI y offset 16
Setup auto-login, auto-start of mythfrontend
URL http://www.mythtv.org/wiki/index.php/Frontend_Auto_Login
Tried ratpoison, Gnome and KDE – ratpoison I couldn’t get working without troubleshooting and Gnome and KDE are too heavy weight. fvwm works well, although the font sizes are a bit small – haven’t found where to adjust them yet.
Use fvwm window manager:
Add to inittab:
c7:12345:respawn:/sbin/mingetty --autologin=mythtv tty7
~mythtv/.bash_profile
if [ -z "$DISPLAY" ] && [ $(tty) == /dev/tty7 ]; then
while [ 1 == 1 ]
do
startx
sleep 10
done
fi
HOLD
Use ratpoison window manager:
Add to inittab:
c7:12345:respawn:/sbin/mingetty --autologin=mythtv tty7
~mythtv/.bash_profile
if [ -z "$DISPLAY" ] && [ $(tty) == /dev/tty7 ]; then
while [ 1 == 1 ]
do
startx
sleep 10
done
fi
.xinitrc:
xset -dpms s off
xsetroot -solid black
ratpoison &
x11vnc -many -q -bg -rfbauth .vnc/passwd
mythfrontend > /home/mythtv/mythfrontend.log 2>&1
for i in 5 4 3 2 1 ; do
if [ -f mythfrontend.log.$i ]; then
mv -f mythfrontend.log.$i mythfrontend.log.$(($i + 1))
fi
done
mv mythfrontend.log mythfrontend.log.1
.ratpoisonrc:
# This is a sample .ratpoisonrc file
#
# Set the prefix key to that of screen's default
escape C-a
# put something informative on the screen while we load stuff
exec xloadimage -onroot -quiet -center /home/mythtv/.mythtv/mythtvstart.jpg
# Gets rid of that ugly crosshairs default cursor and set the background to black
exec xsetroot -cursor_name left_ptr
# Use the name of the program rather than the title in the window list
defwinname name
### fire up an xterm with ctrl-A x
bind x exec xterm -j -fn '*-courier-*-r-*-14-*'
# Since running a 720x576 definition the ratpoison screens are too big for the
# display so we reduce the size of them with defpadding to make them fit
#defpadding 25 25 25 25
keystate_numlock = enable
KDE application file into ~mythtv/.kde/Autostart
Had to setup desktop for mythtv (all black, no screen saver)
Migrate from 120GB disk back to 320GB SATA
2007/10/20 Fedora 7
Use LVM to move the data, including /root, swap and /storage
In BIOS, enable SATA drive, position as HDD #2 (120GB IDE as HDD #1)
Boot single user (interrupt grub, select first kernel <e>dit, select kernel spec line, <e>dit, add “single” on the end of the line, <b>oot the system (off the old IDE disk)
Display partition table for both drives just to be sure that the 320GB (new) disk is /dev/sbd and the current ‘production’ IDE disk is /dev/sda
# fdisk -l /dev/sda
# fdisk -l /dev/sdb
Zero out the partition table and MBR on the SATA disk as we had previously installed Fedora 7, and that data will confuse the migration process.
# dd if=/dev/zero of=/dev/sdb bs=1024k count=100
Partition new disk to add similar partition structure, including LVM partition
sdb1 100MB ext3 /boot (0x83)
sdb2 <the rest> LVM (0x8e)
Set the disk bootable (option a)
[root@mythtv ~]# fdisk -l /dev/sdb
Disk /dev/sdb: 250.0 GB, 250059350016 bytes
255 heads, 63 sectors/track, 30401 cylinders
Units = cylinders of 16065 * 512 = 8225280 bytes
Device Boot Start End Blocks Id System
/dev/sdb1 * 1 13 104391 83 Linux
/dev/sdb2 14 30401 244091610 8e Linux LVM
Zero out the LVM partition as we had already setup a fresh Fedora 7 install, and the LVM information will still be there (and called VolGroup00, it will confuse LVM on the old IDE disk)
# dd if=/dev/zero of=/dev/sdb2 bs=1024k count=100
Copy the /boot contents across:
# mkfs.ext3 /dev/sdb1
# mkdir /tmp/new
# mount /dev/sdb1 /tmp/new
# cd /boot
# find . –print | cpio –pmd /tmp/new
Now update (install) boot loader on new 320GB disk:
# mount /dev/sdb1 /tmp/new (if not still mounted)
# mv /tmp/new/grub/device.map /tmp/new/grub/device.map.old
# /sbin/grub-install /dev/sdb
# umount /tmp/new
Label this filesystem as /boot to match /etc/fstab:
# e2label /dev/sdb1 /boot
Now ‘create’ the new physical volume in LVM and display the pv’s to ensure all’s good:
# pvcreate /dev/sdb2
# pvdisplay
Add the new physical volume into the VolGroup00 volume group
# vgextend VolGroup00 /dev/sdb2
Move all the physical extents from the old IDE disk to the new SATA disk (this will tell lvm to move the physical extents from PV /dev/sda2 to some other free physical volume – the only other volume is the SATA disk we just added). Note this will take a LONG time and will display it’s progress:
# pvmove /dev/sda2
Remove the old disk:
# pvremove /dev/sda2
Power off and disconnect power to the old IDE disk, boot to ensure all comes up ok
Power off and remove IDE
HOLD Get firmware for Hauppauge PVR-350
http://ivtvdriver.org/index.php/Firmware
Firmware files (Video 4 Linux):
v4l-cx2341x-enc.fw
v4l-cx2341x-enc.fw
v4l-cx2341x-init.mpg
Place in hot plug directory for ivtv to get and load into the PVR-350 on boot:
/lib/firmware/v4l-cx2341x-dec.fw
/lib/firmware/v4l-cx2341x-enc.fw
/lib/firmware/v4l-cx2341x-init.mpg
Example of missing fw in dmesg:
Sep 5 16:02:29 mythtv kernel: ivtv: ==================== START INIT IVTV ====================
Sep 5 16:02:29 mythtv kernel: ivtv: version 1.0.0 (2.6.22.4-65.fc7 SMP mod_unload 686 4KSTACKS ) loading
Sep 5 16:02:29 mythtv kernel: eth0: forcedeth.c: subsystem: 01462:7252 bound to 0000:00:14.0
Sep 5 16:02:29 mythtv kernel: ACPI: PCI Interrupt Link [LNKA] enabled at IRQ 19
Sep 5 16:02:29 mythtv kernel: ACPI: PCI Interrupt 0000:04:08.0[A] -> Link [LNKA] -> GSI 19 (level, low) -> IRQ 20
Sep 5 16:02:29 mythtv kernel: firewire_ohci: Added fw-ohci device 0000:04:08.0, OHCI version 1.10
Sep 5 16:02:29 mythtv kernel: ivtv0: Autodetected Hauppauge card (cx23415 based)
Sep 5 16:02:29 mythtv kernel: ACPI: PCI Interrupt Link [LNKC] enabled at IRQ 18
Sep 5 16:02:29 mythtv kernel: ACPI: PCI Interrupt 0000:04:06.0[A] -> Link [LNKC] -> GSI 18 (level, low) -> IRQ 21
Sep 5 16:02:29 mythtv kernel: firewire_core: created new fw device fw0 (0 config rom retries)
Sep 5 16:02:29 mythtv kernel: ivtv0: unable to open firmware v4l-cx2341x-enc.fw (must be 376836 bytes)
Sep 5 16:02:29 mythtv kernel: ivtv0: did you put the firmware in the hotplug firmware directory?
Sep 5 16:02:29 mythtv kernel: ivtv0: Retry loading firmware
Sep 5 16:02:29 mythtv kernel: ivtv0: unable to open firmware v4l-cx2341x-enc.fw (must be 376836 bytes)
Sep 5 16:02:29 mythtv kernel: ivtv0: did you put the firmware in the hotplug firmware directory?
Sep 5 16:02:29 mythtv kernel: ivtv0: Error initializing firmware
Sep 5 16:02:29 mythtv kernel: ivtv0: Error -19 on initialization
Sep 5 16:02:29 mythtv kernel: ivtv: ==================== END INIT IVTV ====================
Example of initialization of fw in dmesg:
Linux video capture interface: v2.00
ivtv: ==================== START INIT IVTV ====================
ivtv: version 1.0.0 (2.6.22.4-65.fc7 SMP mod_unload 686 4KSTACKS ) loading
eth0: forcedeth.c: subsystem: 01462:7252 bound to 0000:00:14.0
ACPI: PCI Interrupt Link [LNKA] enabled at IRQ 19
ACPI: PCI Interrupt 0000:04:08.0[A] -> Link [LNKA] -> GSI 19 (level, low) -> IRQ 20
firewire_ohci: Added fw-ohci device 0000:04:08.0, OHCI version 1.10
ivtv0: Autodetected Hauppauge card (cx23415 based)
ACPI: PCI Interrupt Link [LNKC] enabled at IRQ 18
ACPI: PCI Interrupt 0000:04:06.0[A] -> Link [LNKC] -> GSI 18 (level, low) -> IRQ 21
firewire_core: created new fw device fw0 (0 config rom retries)
ivtv0: loaded v4l-cx2341x-enc.fw firmware (3730290280 bytes)
ivtv0: loaded v4l-cx2341x-dec.fw firmware (3730290288 bytes)
ivtv0: Encoder revision: 0x02060039
ivtv0: Decoder revision: 0x02020023
tveeprom 2-0050: Hauppauge model 48132, rev K268, serial# 9868627
tveeprom 2-0050: tuner model is LG TAPE H001F MK3 (idx 68, type 47)
tveeprom 2-0050: TV standards NTSC(M) (eeprom 0x08)
tveeprom 2-0050: audio processor is MSP4448 (idx 27)
tveeprom 2-0050: decoder processor is SAA7115 (idx 19)
tveeprom 2-0050: has radio, has IR receiver, has no IR transmitter
ivtv0: Autodetected Hauppauge WinTV PVR-350
tuner 2-0043: chip found @ 0x86 (ivtv i2c driver #0)
tda9887 2-0043: tda988[5/6/7] found @ 0x43 (tuner)
tuner 2-0061: chip found @ 0xc2 (ivtv i2c driver #0)
saa7115 2-0021: saa7115 found (1f7115d0e100000) @ 0x42 (ivtv i2c driver #0)
saa7127 2-0044: saa7129 found @ 0x88 (ivtv i2c driver #0)
msp3400 2-0040: MSP4448G-A2 found @ 0x80 (ivtv i2c driver #0)
msp3400 2-0040: MSP4448G-A2 supports radio, mode is autodetect and autoselect
tuner 2-0061: type set to 47 (LG NTSC (TAPE series))
ivtv0: Registered device video0 for encoder MPEG (4 MB)
ivtv0: Registered device video32 for encoder YUV (2 MB)
ivtv0: Registered device vbi0 for encoder VBI (1 MB)
ivtv0: Registered device video24 for encoder PCM audio (1 MB)
ivtv0: Registered device radio0 for encoder radio
ivtv0: Registered device video16 for decoder MPEG (1 MB)
ivtv0: Registered device vbi8 for decoder VBI (1 MB)
ivtv0: Registered device vbi16 for decoder VOUT
ivtv0: Registered device video48 for decoder YUV (1 MB)
ivtv0: loaded v4l-cx2341x-init.mpg firmware (3730291512 bytes)
ivtv0: Initialized Hauppauge WinTV PVR-350, card #0
ACPI: PCI Interrupt Link [LAZA] enabled at IRQ 22
ACPI: PCI Interrupt 0000:00:10.1[B] -> Link [LAZA] -> GSI 22 (level, low) -> IRQ 18
PCI: Setting latency timer of device 0000:00:10.1 to 64
ivtv: ==================== END INIT IVTV ====================
As per http://wilsonet.com/mythtv/fcmyth.php?SID&expandables=closed&ivtv=open&pvr350out=open#capture:
Alternatively, use yum to install from the ATrpms repository
# yum install ivtv-firmware
Get DVD libraries
Download from ATrpms:
libdvdcss-1.2.9-3.fc7.i386.rpm
# rpm –install libdvdcss-1.2.9-3.fc7.i386.rpm
If I missed anything post a reply to this thread & I’ll add your updates.
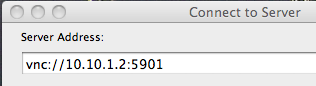 Within Finder, either use Go -> Connect to Server or Apple-K to bring up the Connect to Server window. The server address is the URL that points to the Ubuntu VNC instance
Within Finder, either use Go -> Connect to Server or Apple-K to bring up the Connect to Server window. The server address is the URL that points to the Ubuntu VNC instance 
